In Singapore’s Cybersecurity Awareness Month in Oct, various data breaches impacting organizations large and small were reported. High-profile incidents included Australian telcos Optus and Telstra, eight Shangri-La hotels around Asia, health insurance provider Medibank, online retailers MyDeal and Vinomofo .
In late September 2022, Optus, Australia’s second largest telco is breached. It has been revealed that 2.1 million personal identification numbers have been stolen with 30,000 of its current and former employee details leaked as well. In early October, Telstra had 18.8 million of its accounts stolen. There was another data breach earlier last week in Australia’s biggest health insurance provider Medibank, which led to 200GB worth of confidential data being stolen. Another major cybersecurity incident occurred at MyDeal just a day after the Medibank data breach. MyDeal has confirmed that the data of around 2.2 million customers has been breached.
With today’s sophisticated hackers, no business is safe from data breaches. Small and medium-sized enterprises (SMEs) often have leaner cybersecurity teams and budgets and lack effective cyber security strategies. Cyber criminals are aware of the fact that SMEs are often easier targets. It is a misconception that SMEs are spared from cyber criminals.
So how can you stop this from happening to your company? In this article, we will discuss five solidly proven ways to prevent cyber disaster from occurring at your organisation.
1. Beware Shadow IT
Gartner refers to shadow IT as “IT devices, software and services outside the ownership or control of IT organizations”. Training the users on the risk of shadow IT and having the IT team be able to support the needs of the business is extremely important. Gone were the days which IT folks can ask users to wait weeks or months to get a service up, because most people would simply use google to find out if the service was available for them to use online. It would be a major plus point if these services are free, but in our current modern world that values data more then any other thing, are free services truly free?
2. Automate certificate services
Certificates are used everywhere, in your websites, on your email, when you do a VPN or when your administrators log into a web portal to perform actions on hardware devices. We see a trend of maturity where larger organisations create a central Public Key Infrastructure(PKI) service to centralise control over all certificate usage. This central PKI service issues certificate for the entire organisation and provides the gateway devices the ability to block any self-signed services reducing the risk that was previously mentioned. The next step would then be the automation of not just the certificates request via self-service but the renewal of these certificates as well. Netrust is a well-known Singapore Certificate Authority that would be able to help with this.
3. Uncover the internal threats early
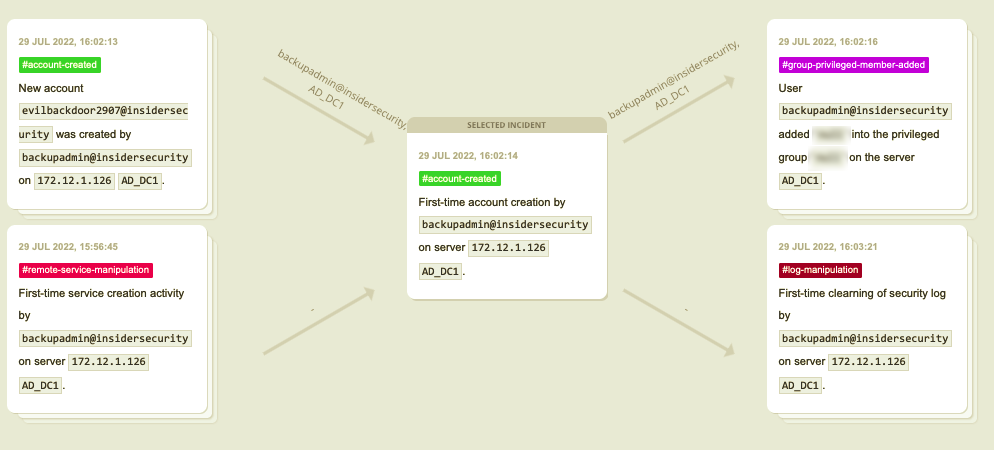
User and Entity Behaviour Analytics (UEBA) has emerged as the most effective approach to comprehensively detect a far wider range of real-time suspicious activities and unknown threats in the enterprise.
InsiderSecurity’s Automated UEBA applies algorithms, scenario analytics and advanced machine learning rather than rules or signatures to provide crucial visibility and risk score of suspicious activity. It reduces response time to cyber attacks. Based on advanced analytics of user behavior, our automated UEBA provides increased security coverage with minimal investment for security experts in SMEs.
For example, consider this attack scenario. There is a zero-day vulnerability in your systems, which is not yet known to the public but is already being actively exploited by attackers. InsiderSecurity’s Automated UEBA is able to uncover such an attack by monitoring for the suspicious account and network activity in the systems and alert you early.
4. Secure the database server
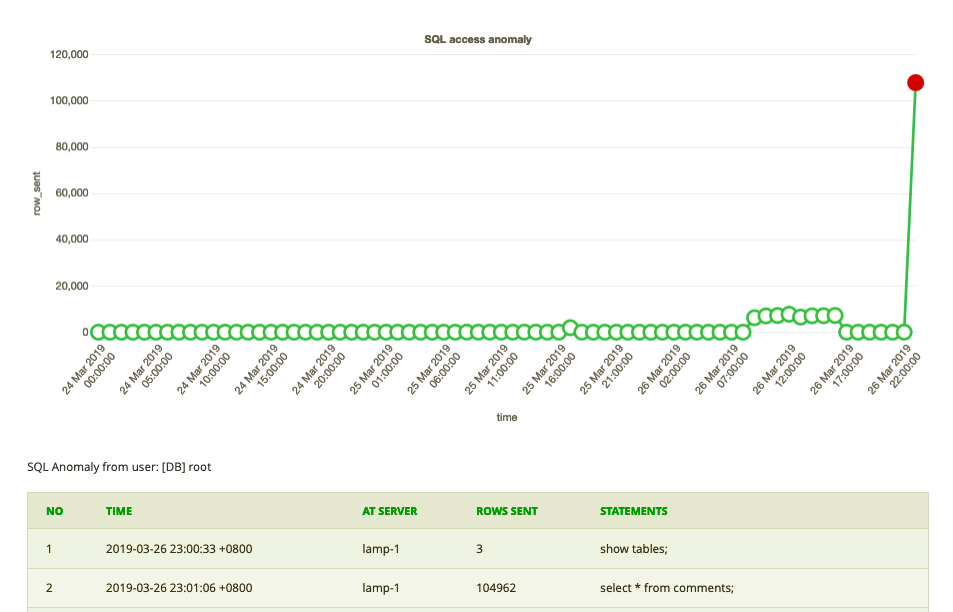
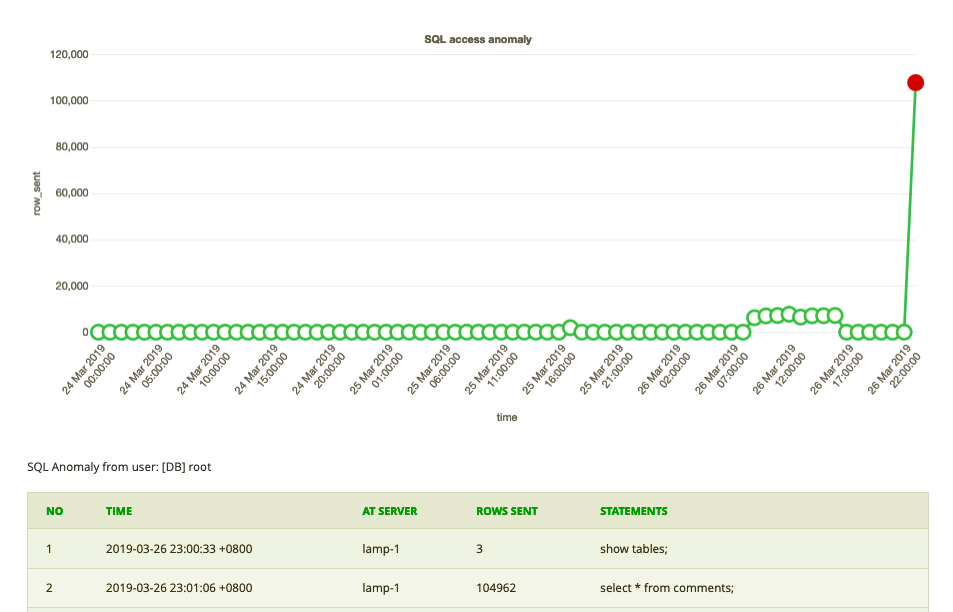
Database Activity Monitor is a critical aspect of minimizing your company’s risks and protecting not only your data but also company’s reputation. For organizations with sensitive databases, InsiderSecurity’s Database Activity Monitor automatically discovers suspicious data access and data theft early. This leverages on InsiderSecurity’s AI-driven cybersecurity analytics. Database Activity Monitor works out-of-the-box as users do not need to configure complex rules. Furthermore, Database Activity Monitor helps meet data protection regulations such as PDPA and GDPR.
After attackers or rogue insiders gained initial access in a victim’s infrastructure, they will move laterally around the internal IT systems and attempt to access high-value data stored in the enterprise’s databases. InsiderSecurity’s Database Activity Monitor can discover such database access early before there is serious data loss.
5. Ensure data security in cloud services
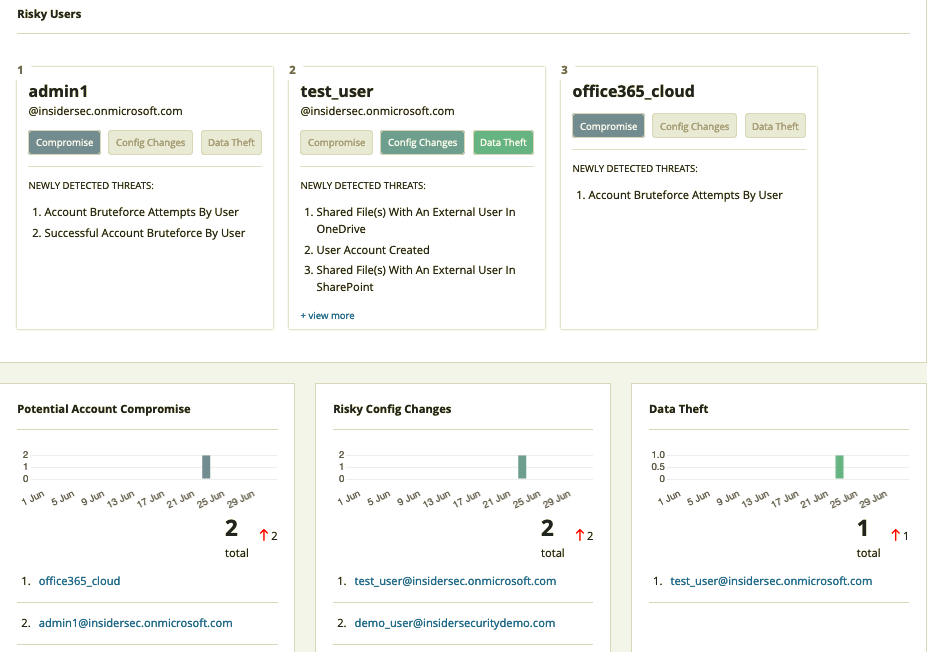
To safeguard against the ever-evolving cloud threats, consider implementing InsiderSecurity’s Cloud Security Monitor (CSM) for managing cloud access and securing the cloud workspace. It is a simple-to-use SaaS to monitor data security in cloud services. CSM detects suspicious data access and new and emerging threats with behavioral analytics. It applies machine-built timelines to decrease response times and improve analyst productivity by automating incident investigation. CSM also monitors for compromised Microsoft 365 accounts and discovers documents shared to the public by accident.
Attackers are known to do this: after compromising an on-premise network, the attackers are able to steal the cloud credentials to access the victim’s cloud infrastructure and gain access to sensitive documents in OneDrive or SharePoint. With InsiderSecurity’s Cloud Security Monitor, such threat behaviour can be detected early to mitigate further damage.
Summary
In the past 10 years, the number of data breaches has increased significantly. Protecting the business from these threats is essential. Protect your company by implementing the approaches described above.
Clearly understanding the possible danger from shadow IT and the benefits of certificate automation are vital for ensuring the proper security of your organization’s critical assets. Netrust is a well-known Certificate Authority that provide such certificate services, please reach out to Netrust Pte Ltd at sales@netrust.net or visit https://www.netrust.net/ if you would like to find out more.
The other key is to be able to detect the breach early. Detecting the breach early enables a company to minimize or prevent data loss altogether and avoid a cyber disaster. InsiderSecurity’s award-winning solutions help you to do this.